Are your emails being delivered to the inbox? Do you have a handle on email authentication protocols like SPF, DKIM, and DMARC? If not, now is the time to get up-to-speed with these important email security principles.
Email marketer specialists, as well as advertising and marketing agencies, need to ensure their emails are not only reaching the right recipients but are also secure.
Configuring SPF, DKIM, and DMARC correctly can help protect your business from malicious attacks while ensuring that emails sent by you reach their intended destination quickly and safely.
In this blog post, we will explain each of these authentication techniques in more detail so that you can feel confident about putting them into practice for your own brand or client campaigns!
Let’s figure out what needs to be done to prevent emails from going to spam.
SPF, DKIM, and DMARC are the basic settings that you must make before starting email marketing, no matter which mailing service you choose. Without them, the letter will not be delivered to the client’s mailbox or will end up in the “Spam” folder.
What is an SPF record and why do you want to set it?
Sender Policy Framework (SPF) is a security mechanism that informs your prospects that the message you sent is safe and you’re a trustworthy sender. SPF authenticates your domain and therefore protects your domain’s good reputation.
An SPF record looks like this:
v=spf1 ip4:176.57.223.0/24 -all
🔹 where v — SPF version, always takes the value v=SPF1;
🔹 ip4 — IP address from which sending emails is allowed;
🔹 -all – mechanism for working with letters sent from other IP addresses.
This SPF record is simple and very strict. It allows sending emails only from the specified IP. All other messages should be blocked, as the “-all” mechanism is specified.
How an SPF record works
After the message is sent, the recipient’s mail server checks which IP address the message came from. He checks it against the list that is written in the SPF.
If the address is on the list, then everything is in order. The letter goes into the inbox. If the IP address is not in the list, then the email may be blocked by the mail provider

But if the SPF is not registered, there is a high probability that the letter will be delivered. And then scammers can easily write a message on your behalf and steal the personal data of subscribers.
What is an SPF record for?
Domain protection from spoofing.
The main reason to set up SPF is to keep your domain secure.
Sometimes scammers send letters on behalf of another company or person, disguise themselves as a well-known brand, send messages “from the bank” about the transfer of funds and ask to follow the link. They do this to steal user data, money from a card, or to plant a virus program on a computer.
A scheme in which the sender of an email tries to impersonate someone else, uses someone else’s logo and a similar email address, is called a spoofing attack. To protect corporate mail and domain from blocking, and your subscribers from fraudsters, you need to configure SPF. Then the substitution of the sender will be less scary.
Delivery of letters to the inbox.
Mail providers are loyal to senders who have set up email authentication, including SPF. Mailers are more likely to miss letters from such companies in the inbox.
Additional features.
If you have added an SPF record, you will be able to connect advanced statistics services for sent mailings – postmasters. True, for this you still need to configure DKIM.
SPF record mechanisms
Any SPF record starts with v=spf1, this value does not change.
Next are the parameters, or mechanisms. The following are most often used: all, ip4, ip6, a, mx, include, redirect.
The “ip4/ip6” parameters specify specific addresses from which you can send emails. The “a” parameter checks the A-record of the domain, “mx” – the MX-record of the domain.
The domain A record is responsible for linking to the server’s IP address. If the A-record is not registered, the site will not work. But the MX record is responsible for the server through which the mail works.
The include, redirect mechanisms allow you to apply the SPF settings of another domain. They are used by companies that have multiple domains and mail servers. Then you can register the SPF settings once and thereby simplify the work.
The “all” parameter specifies the processing of all messages from addresses not specified in the SPF record. How exactly the mailer will deal with these letters depends on the prefix written in front of the parameter.
Prefixes (or qualifiers) dictate the actions to be taken on the sender’s emails:
“+” – pass, receive mail.
“-” – fail, reject mail.
“~” – softFail, accept mail, but put it in spam.
“?” – to process as the usual letter.
A couple of examples:
v=spf1 a include:other-domain.com -all
Receive mail from the A-record of the current domain and servers specified in the SPF-record of the other-domain.com domain. Reject all other letters.
v=spf1 ip6:2002:db7 ~all
Receive mail from the specified address, send other letters to spam.
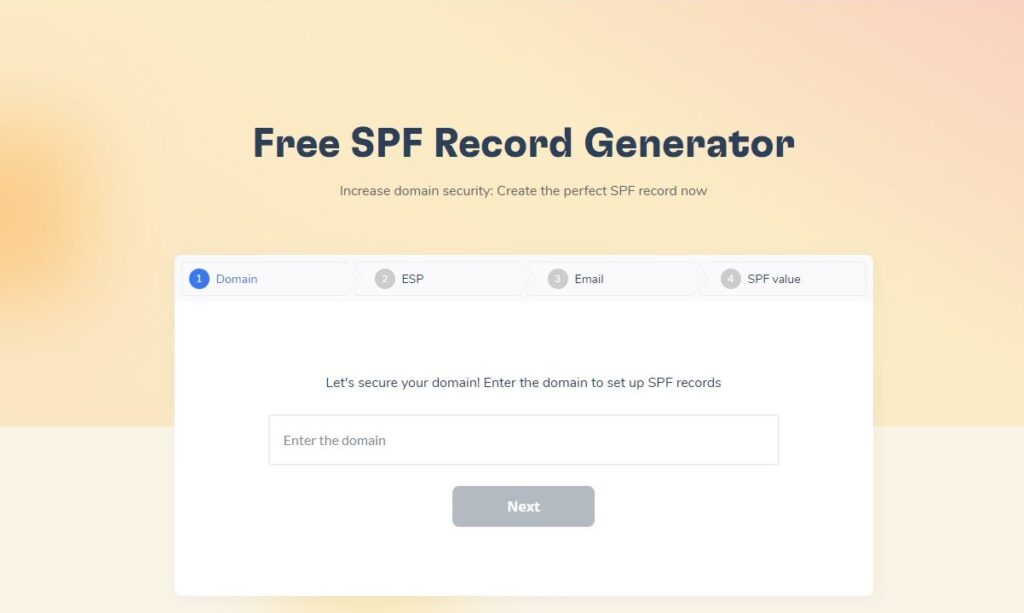
Take the first step towards securing your email delivery with Warmy’s Free SPF Record Generator. Our user-friendly tool simplifies the creation of SPF records to protect your domain against spoofing and ensure your emails reach their intended destination. Don’t let your messages get sidelined by spam filters. Visit Free SPF Record Generator and fortify your email authenticity today. It’s quick, easy, and absolutely free!
How to set up SPF for mailings?
After setting up an SPF signature, it’s worth checking if it works correctly. This can be done using our service, if your mailbox is connected to Warmy, or using third-party services, such as Mailtester.
MailTester.com – a service with which you can test a letter, including verifying the SPF signature. MailTester gives you a complete deliverability report and also checks your email authentication settings.
You will be prompted to send a test email to the provided email address, after which you will be able to receive a detailed report about your mailbox.
All this will be evaluated on a scale from 1 to 10, where 1 – you are most likely to land in the SPAM folder, and 10 – you will definitely get into your recipient’s Inbox. DMARC is an algorithm of actions with your mailings if messages are found suspicious. All of these security elements are created as TXT, a DNS record type that allows textual information to be associated with a domain.
SPF confirms that the domain is not fake.
Sender Policy Framework is an entry with a list of servers and IP addresses from which it is allowed to send messages on behalf of the domain. By setting up SPF, you inform the mail services that it was you who sent the letter. If the letter is sent from an IP or server that is not in the record, the provider will regard it as spam.
To set up SPF, create a text record of the servers from which you send mailings. Settings are made in the domain hosting control panel. For example, if your domain is hosted with UltaHost, you can manage SPF records directly from the UltaHost DNS manager.
What is DKIM and how to setup it?
DomainKeys Identified Mail (DKIM) is a way to authenticate and protect your domain. DKIM helps to safely deliver your messages to your prospects.
DKIM (DomainKeys Identified Mail) is an email verification technology that can be used to detect fake emails. DKIM adds a digital signature to the email. Thanks to it, mail providers can check that the message was sent from the specified domain.
A DKIM signature is a TXT record that is added to the site’s DNS zone settings. The entry itself looks like this:
us._domainkey TXT v=DKIM1; k=rsa; p=XXXXXXXXXXXXXXXXXXXXX,
🔹 where v — DKIM version, always takes the value v=DKIM1;
🔹 k — key type, always k=rsa;
🔹 p — unique code that can be generated in the mailing service.
Why do you need a DKIM signature?
Navigating the complexities of the Spamhaus DROP List and successfully delisting your IP address is a journey that requires understanding, diligence, and proactive measures. Through this guide, “Guide to Delisting Your IP from Spamhaus DROP: A Step-by-Step Approach,” we’ve explored the essential steps from understanding what the DROP List is, to checking your IP status, engaging in the delisting process, and implementing post-delisting actions.
Remember, being listed on the Spamhaus DROP List is not just a technical issue; it impacts your email deliverability, your business communications, and ultimately, your online reputation. Therefore, the importance of regularly monitoring your IP status, adhering to best email practices, and using effective tools like Warmy.io cannot be overstated.
We hope this guide has provided you with valuable insights and actionable steps to manage your IP’s reputation effectively. Remember, in the realm of digital communication, your IP’s health is integral to your success. Stay informed, stay proactive, and keep your IP off the Spamhaus DROP List.
Protects from scammers
A DKIM signature will prevent spammers from sending emails on your behalf. Together with SPF and DMARC, this technology will protect your subscribers from fraudsters, including identity theft.
Increases deliverability
DKIM improves domain reputation. Using DKIM, the receiving server determines the authenticity of the sender and its overall rating. Emails with a good reputation are more likely to end up in the inbox.
DKIM works like an ID: you present it to the mail provider, and he lets you into the inbox.
Gives access to postmasters
Postmasters are mail services for mailing analytics. They help track deliverability, opens, unsubscribes, and spam complaints. To enable statistics in the postmaster, you must have email authentication configured. DKIM is one of the components of email authentication.
How DKIM works?
DKIM works like this: the letter contains encrypted data about who and when the letter was sent. The mail provider receives this data along with the letter. The provider decrypts them using the public key posted on the domain from which the letter was sent. If the data matches, then this is an honest sender, the letter can be skipped to the Inbox. If not, it is a scammer, the letter goes to Spam.

How to set up a DKIM signature?
To set up DKIM, you need access to the site’s DNS zone and corporate email. Typically, SPF and DKIM records are generated in the mailing service and added through a personal account on the hosting.
DKIM Signature Verification
After setting up a DKIM signature, it’s worth checking if it works correctly. This can be done using our service, if your mailbox is connected to Warmy, or using third-party services, such as Mailtester.
MailTester.com – a service with which you can test a letter, including verifying the DKIM signature. MailTester gives you a complete deliverability report and also checks your email authentication settings.
You will be prompted to send a test email to the provided email address, after which you will be able to receive a detailed report about your mailbox.
All this will be evaluated on a scale from 1 to 10, where 1 – you are most likely to land in the SPAM folder, and 10 – you will definitely get into your recipient’s Inbox.
What is DMARC?
DMARC (domain-based message authentication reporting and conformance) is a policy to protect users from spam and phishing emails.
Why is a DMARC policy needed?
DMARC allows you to resist phishing – fraud, the purpose of which is to steal confidential user data (logins, passwords, credit card information). The main phishing tool is email letters. Typically, attackers disguise their messages as messages from well-known companies using their domains. If the user follows the instructions from such a letter, he loses personal data and often money. And the company suffers significant reputational damage.
If the company has DMARC configured, then the email sent by scammers on its behalf will either not be delivered at all or will be marked as suspicious.

How DMARC works?
DMARC is a protocol that tells the server what to do with the message if the DKIM and SPF records are incorrect. Correct DKIM and SPF confirm that the email was sent from the domain specified in the “From:” field in the email.
Thus, DMARC, along with SPF and DKIM, is responsible for mail authentication. That is, for the sender authentication procedure.
Let’s see how these records differ.
DKIM works like this: the letter contains encrypted data about who and when the letter was sent. The mail provider receives this data along with the letter. The provider decrypts them using the public key posted on the domain from which the letter was sent. If the data matches, then this is an honest sender, and the letter can be skipped to the Inbox. If not, it is a scammer, the letter goes to Spam.
SPF indicates whether a particular server is allowed to send emails from that domain. The server is identified by its IP address. For example, when you send a Campaign using a cold mailing service or set up corporate mail, you delegate the provider’s and service’s servers the right to send emails from your domain. SPF detects a trusted sender by IP
Now let’s deal with DMARC. This entry:
✔ tells the mail provider what to do with the message depending on the results of reading DKIM and SPF;
✔ tells the server to send a report to the mail of the domain administrator (that is, you or your system administrator) with information about what letters were sent and how the provider dealt with the letters.
How the provider checks emails based on DMARC settings?
After your email is received by the recipient’s provider, it checks the reputation of the domain, the presence of the email and the domain in the blacklists, the IP addresses of the servers from which the email was sent.
As part of this check, the mail provider:
1. Decrypts and verifies DKIM. Is the letter sent from this domain exactly, or is it a fake.
2. Decrypts and verifies SPF. Is it allowed to send emails on behalf of this domain to this IP.
3. Applies the policy specified in DMARC. Let’s say DMARC says to “Spam” those whose DKIM does not match and send a report about it to the domain administrator.
4. Next, standard spam filters are applied to the message.
Options for the development of events after verification:
– The letter is skipped and ends up in the Inbox. If DKIM and SPF are OK and spam filters are passed.
– The message has been quarantined (in “Spam”). If DKIM does not match and/or spam filters are not passed.
– The letter was rejected (not delivered). Individual reasons: for example, the user’s mailbox is full.
After the distribution of letters, an automatic report is sent to the sender, which says what happened to the sent letters.
How to set up DMARC?
1. Go to your website’s hosting control panel.
2. Find DNS records management in the settings.
3. Enter a new DMARC TXT record. A TXT record is a type of DNS record in text format that tells external sources what to do. We have listed the most common entries in the examples below. You can copy the entry from there.
4. Save your changes.
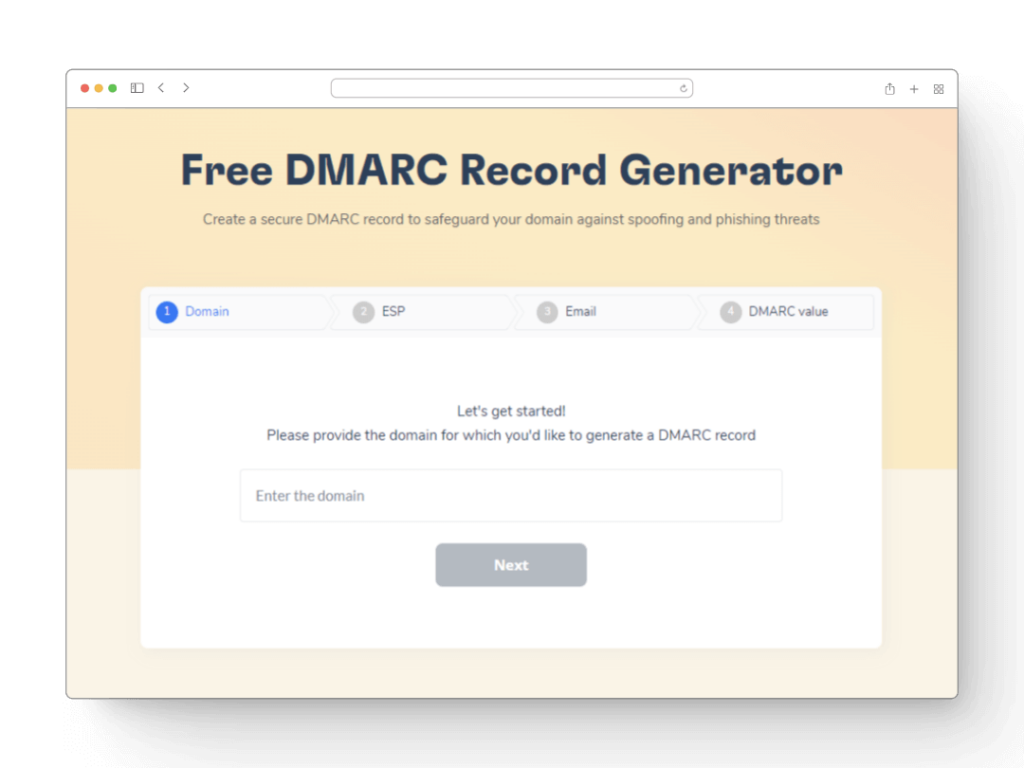
Looking to boost your email security for free? Warmy’s new DMARC Generator is your solution! Easy to use and absolutely free. Explore it today – Free DMARC Record Generator
Why is a DMARC policy needed?
DMARC tags are either required or optional. The required ones are v=DMARC1 and p= with the policy value.
“v=DMARC1; p=none;”
🔹 v=DMARC1 — version of the DMARC protocol, must be 1. The record allows the provider to recognize that it is this TXT record that defines the DMARC policy. If this parameter does not come first in the entry, DMARC is not recognized.
🔹 p is the Requested Mail Receiver Policy, that is, what exactly to do with the letter if DKIM did not pass the check.
A policy can have three values:
– p=none – take no special action, or everything is at the discretion of the mail provider;
– p=quarantine — send to Spam;
– p=rejected – do not accept the letter.
In addition to the required tags, you can specify additional ones. They will indicate which reports and where to send, or what percentage of emails to apply the policy to.
Here are the optional tags:
– aspf and adkim allow you to check SPF and DKIM and can take the values r (relaxed) – soft check and s (strict) – strict; first, choose a soft check so as not to block incorrectly configured, but necessary letters from your domain, for example, automatic sending of invoices from 1C;
– pct is responsible for % of messages to be filtered by this protocol. If not filled, all messages will be filtered. If pct=20 – only 20% of emails.
– sp is a subdomain policy (or subdomains), which works in the same way as a domain policy. When you do a bulk mail, mail is sent from different subdomains on your domain. You can control each of them.
– rua – email, which once a day will receive an aggregated report in XML. This report will help you find out who sends emails on your behalf and what emails are generally sent from your domain.
– rf – report if the letter did not pass the check;
– fo – failure reporting options, if the report mechanism did not work:
✔ fo=0 (used by default) — send a report if none of the authentication steps are passed;
✔ fo=1 — if at least one authentication stage is not passed;
✔ fo=d — if DKIM is not passed;
✔ fo=s – if SPF is not passed.
Which DMARC policy to choose?
The hardest part about setting up DMARC is figuring out which policy is right for your current needs.
None is just to deliver all emails. This policy is suitable when you have just started configuring DMARC and want to see who generally sends mail from your domain. You do not know everyone in your company who sends letters, including automatic ones. These can be developers, accounting (which connected 1C), marketers from other departments.
Quarantine is a quarantine policy. With this mark, the letters, depending on the mail provider, will be:
– sent to spam;
– marked for more stringent scrutiny;
– marked as suspicious in the user’s Inbox.
Reject is the strictest policy and the highest level of protection. All emails that fail the SPF and/or DKIM check will be blocked. It would seem that we choose reject and everyone is protected 🙂. But there are nuances here.
DKIM/SPF do not work correctly if:
– users have set up forwarding of letters from one mailbox to another, such letters will not be delivered on your behalf;
– the service through which you send letters, for example, a payment card, does not allow you to register DMARC, DKIM and SPF;
– you forgot to add the mailing service or CRM to the white list of senders, or the white list does not work correctly, then all mass mailings of your choice will not be delivered to users;
– other types of errors and breakages in the DMARC record.
If you set the reject policy, in all these cases, emails will not be delivered to senders.
Experts advise to first write the p=none policy and correct reports into the DMARC policy using the rua and fo tags. The reports will show which addresses emails are sent from and what happens to them. It is possible that you will find fraudulent shipments.
Then think about what needs to be changed in the mailing so that quarantine can be specified in the DMARC policy. This strategy should take into account the interests of all departments that work with the domain and site. It is important to make sure that all emails are configured correctly and SPF, DKIM, DMARC are registered, then emails from accounting or billing will not be marked as suspicious.
DMARC is a great tool for tracking email deliverability and understanding how ISPs receive and process your emails. Based on this, you can improve deliverability and reclaim 5% or more of your base that may not receive emails for technical reasons.
The customer care service helps you set up a DMARC policy for your customers. If you are a Unisender customer, just contact the support chat.
Conclusion
You should now have a better understanding of what SPF, DKIM, and DMARC are and how they work.
You also know why it’s important to configure them for your domain and how to set them up. If you have any questions or need help along the way, our team of experts is here to help – Contact us
We’ll be happy to assist you on your journey to email deliverability success!