How Your Unsubscribe Link Is Making or Breaking Your Deliverability
New research from Warmy reveals how your unsubscribe link configuration directly impacts inbox placement. See the full data…
Turn emails into revenue. Master deliverability, inbox placement, and warm-up strategies to scale outreach while protecting your domain reputation
New research from Warmy reveals how your unsubscribe link configuration directly impacts inbox placement. See the full data…

Email is the lifeblood of modern business – and the favourite hunting ground of cybercriminals. In 2025, more…
How many people actually open and read the emails that you send? Getting your email into the inbox…

What are the best email providers for businesses and startups in 2026? Up to 25% of cold and…
Most B2B teams do not fail at cold email because of messaging alone. They fail because their deliverability…
Most cold email fails before it's even read. In this podcast, learn what actually drives replies in 2026…
Most cold email fails before it's even read. In this podcast, learn what actually drives replies in 2026…
The analytics landscape is hitting a pivot point: we’re seeing a move away from descriptive reporting toward predictive…

Complete AmpiFire AmpCast review with pricing, features & real results. Discover how this AI platform distributes content across…
Compare the best email warmup tools for building and protecting sender reputation. Learn what separates effective tools, what…

Compare top email deliverability tools with customizable warmup schedules. Learn which features matter and find the best solution…
Key takeaways High-volume email warmup requires SPF, DKIM, and DMARC authentication, a clean list, and a dedicated sending…

A Microsoft 365 seed list is a curated set of genuine Microsoft 365 mailboxes that receive your campaign…
We’ve released a new set of API v2 endpoints that give developers and technical users significantly more control…
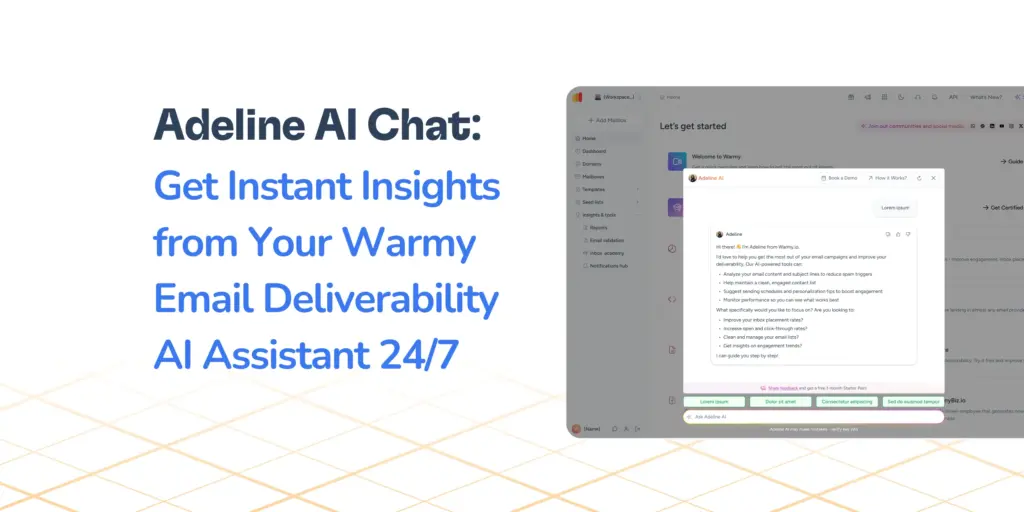
Adeline is Warmy’s built-in AI email assistant, now live inside every user account. In a nutshell, Adeline AI…

Spamhaus can kill your email deliverability overnight. Warmy's 2026 research breaks down every list, what triggers them, and…
This SURBL blacklist report by Warmy.io discusses what triggers a SURBL listing, how to check your domain, and…

The Warmy Research Team breaks down how the Barracuda Reputation Block List works, what triggers an IP listing,…




Talk to an expert